24.4K stars. Most popular pre-commit secret scanner. Community standard for lightweight git-based secret detection.
Gitleaks
active24.4K stars — most-starred secret scanner. 150+ patterns. Fastest pre-commit scanner. The community default for pre-commit secret detection. No official MCP.
Where it wins
24.4K stars — most-starred secret scanner
150+ detection patterns
Fastest pre-commit scanner — lightweight and fast
Community default for pre-commit hooks
Where to be skeptical
No official MCP server
Pre-commit only — no CI/CD verification or runtime interception
Fewer detection patterns than GitGuardian (150 vs 500+) or TruffleHog (800+)
Editorial verdict
Best pre-commit secret scanner. 24.4K stars — most-starred in the category. 150+ patterns, fastest scanner. The community default. No official MCP server — use as pre-commit hook, not agent integration.
Related
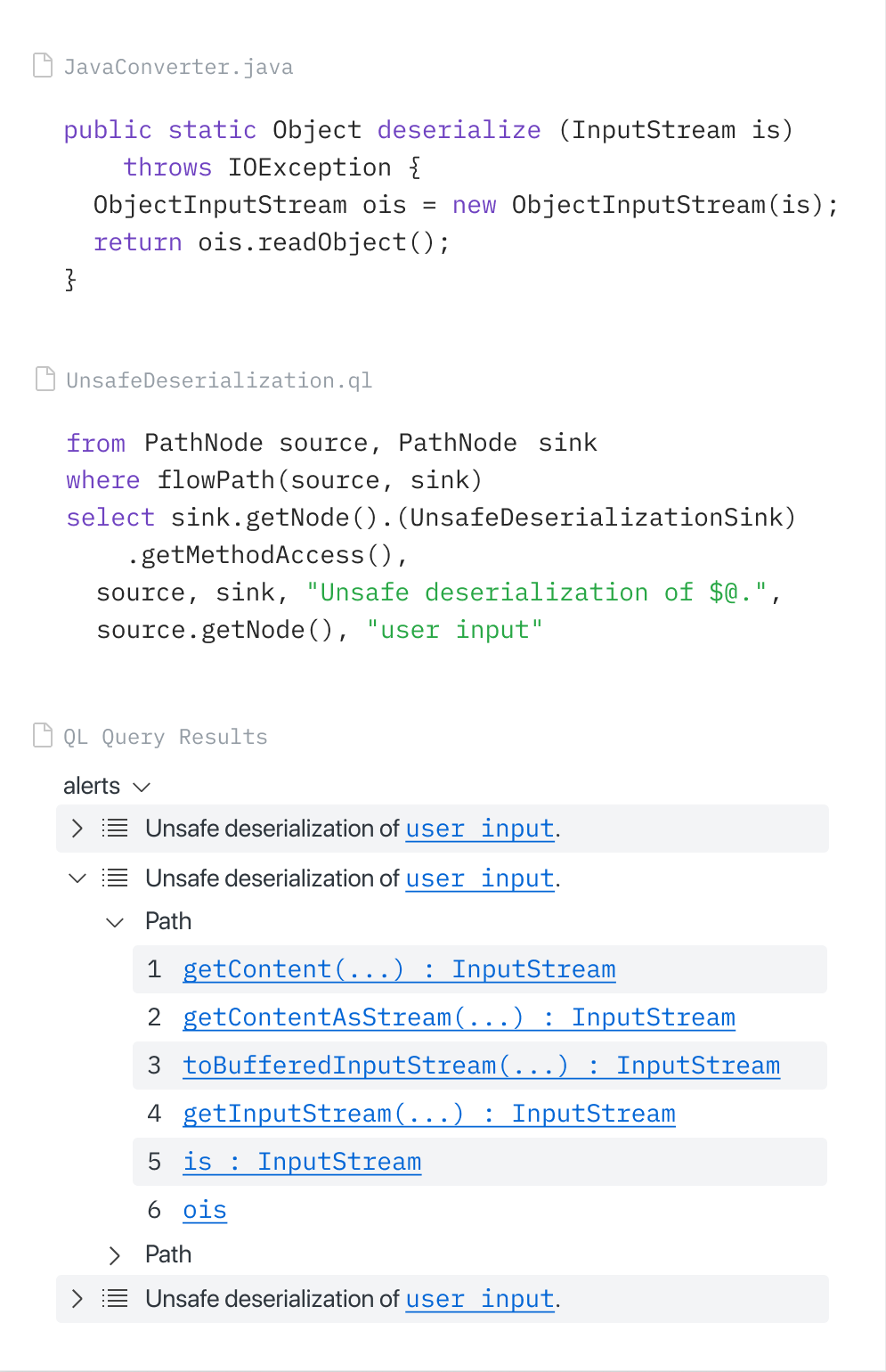
CodeQL (via GitHub MCP Server)
88GitHub-native SAST via CodeQL, accessible through the official GitHub MCP Server. Copilot Autofix generates fixes from CodeQL alerts. GitHub Security Lab Taskflow Agent found ~30 real CVEs. Zero extra setup for GitHub users.
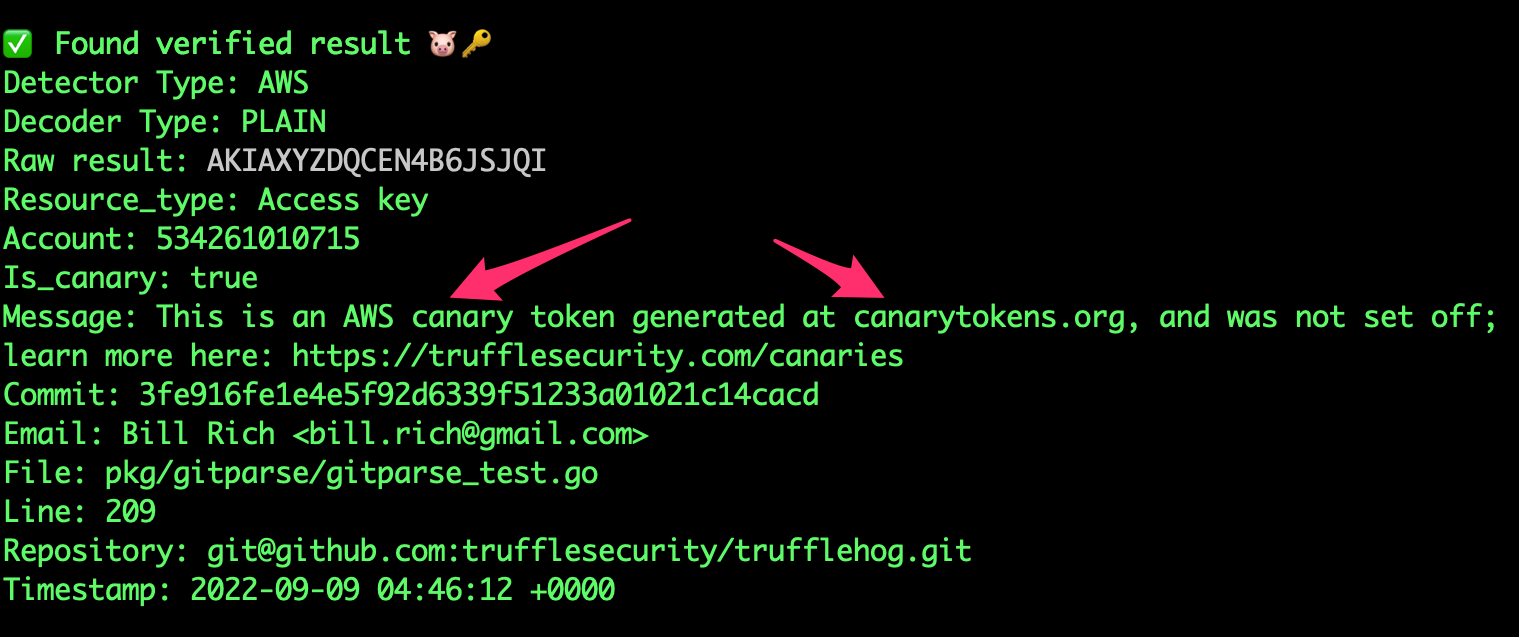
TruffleHog
8818K+ stars. 800+ secret types. Unique credential verification — confirms if leaked creds are still active. Scans S3, Docker, Slack — not just git. No official MCP but community integrations exist.
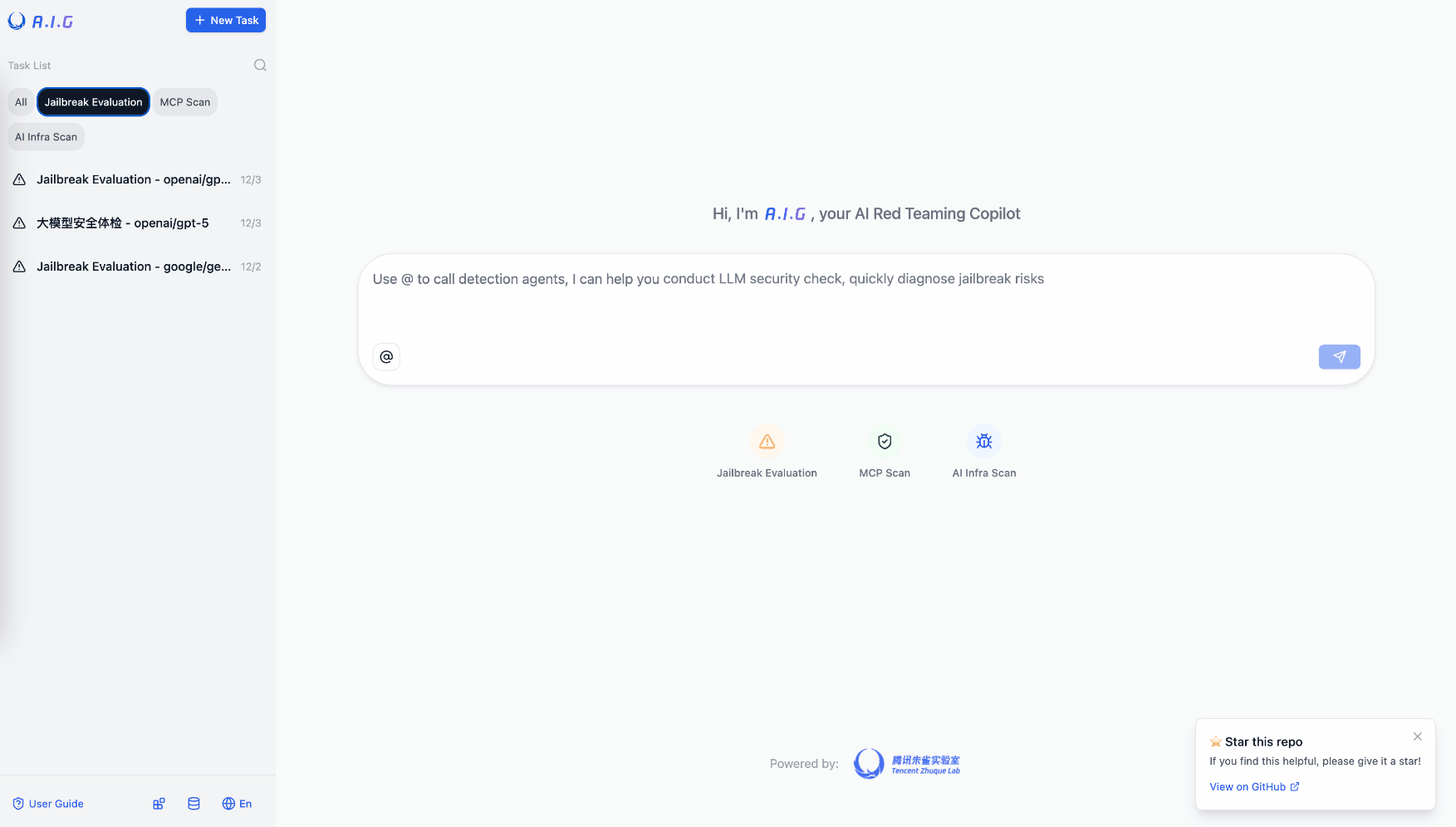
Tencent AI-Infra-Guard
81Most comprehensive OSS AI red teaming tool. 3,264 stars. Full-stack: ClawScan, Agent Scan, Skills Scan, MCP scan, jailbreak eval. 43 AI framework components, 589 CVEs cataloged. v4.0 released.
HexStrike AI
80Dominant offensive security MCP repo. 7,561 stars — largest security MCP repo period. 150+ cybersecurity tools via MCP. Autonomous pentesting, vulnerability discovery, bug bounty automation.
Public evidence
Raw GitHub source
GitHub README peek
Constrained peek so you can sanity-check the source material without leaving the site.
Gitleaks
┌─○───┐
│ │╲ │
│ │ ○ │
│ ○ ░ │
└─░───┘
[!WARNING] Gitleaks is feature complete. I'm not merging new features into Gitleaks. Future releases will be security patches only. I'm shifting my focus to Betterleaks
![Docker Hub][dockerhub-badge]
![Gitleaks Action][gitleaks-badge]
![License][badge-license]
Gitleaks is a tool for detecting secrets like passwords, API keys, and tokens in git repos, files, and whatever else you wanna throw at it via stdin. If you wanna learn more about how the detection engine works check out this blog: Regex is (almost) all you need.
➜ ~/code(master) gitleaks git -v
○
│╲
│ ○
○ ░
░ gitleaks
Finding: "export BUNDLE_ENTERPRISE__CONTRIBSYS__COM=cafebabe:deadbeef",
Secret: cafebabe:deadbeef
RuleID: sidekiq-secret
Entropy: 2.609850
File: cmd/generate/config/rules/sidekiq.go
Line: 23
Commit: cd5226711335c68be1e720b318b7bc3135a30eb2
Author: John
Email: john@users.noreply.github.com
Date: 2022-08-03T12:31:40Z
Fingerprint: cd5226711335c68be1e720b318b7bc3135a30eb2:cmd/generate/config/rules/sidekiq.go:sidekiq-secret:23
Getting Started
Gitleaks can be installed using Homebrew, Docker, or Go. Gitleaks is also available in binary form for many popular platforms and OS types on the releases page. In addition, Gitleaks can be implemented as a pre-commit hook directly in your repo or as a GitHub action using Gitleaks-Action.
Installing
# MacOS
brew install gitleaks
# Docker (DockerHub)
docker pull zricethezav/gitleaks:latest
docker run -v ${path_to_host_folder_to_scan}:/path zricethezav/gitleaks:latest [COMMAND] [OPTIONS] [SOURCE_PATH]
# Docker (ghcr.io)
docker pull ghcr.io/gitleaks/gitleaks:latest
docker run -v ${path_to_host_folder_to_scan}:/path ghcr.io/gitleaks/gitleaks:latest [COMMAND] [OPTIONS] [SOURCE_PATH]
# From Source (make sure `go` is installed)
git clone https://github.com/gitleaks/gitleaks.git
cd gitleaks
make build
Pre-Commit
-
Install pre-commit from https://pre-commit.com/#install
-
Create a
.pre-commit-config.yamlfile at the root of your repository with the following content:repos: - repo: https://github.com/gitleaks/gitleaks rev: v8.24.2 hooks: - id: gitleaksfor a native execution of gitleaks or use the
gitleaks-dockerpre-commit ID for executing gitleaks using the official Docker images -
Auto-update the config to the latest repos' versions by executing
pre-commit autoupdate -
Install with
pre-commit install -
Now you're all set!
➜ git commit -m "this commit contains a secret"
Detect hardcoded secrets.................................................Failed
Note: to disable the gitleaks pre-commit hook you can prepend SKIP=gitleaks to the commit command
and it will skip running gitleaks
➜ SKIP=gitleaks git commit -m "skip gitleaks check"
Detect hardcoded secrets................................................Skipped
Usage
Gitleaks scans code, past or present, for secrets
Usage:
gitleaks [command]
Available Commands:
completion Generate the autocompletion script for the specified shell
dir scan directories or files for secrets
git scan git repositories for secrets
help Help about any command
stdin detect secrets from stdin
version display gitleaks version
Flags:
-b, --baseline-path string path to baseline with issues that can be ignored
-c, --config string config file path
order of precedence:
1. --config/-c
2. env var GITLEAKS_CONFIG
3. env var GITLEAKS_CONFIG_TOML with the file content
4. (target path)/.gitleaks.toml
If none of the four options are used, then gitleaks will use the default config
--diagnostics string enable diagnostics (http OR comma-separated list: cpu,mem,trace). cpu=CPU prof, mem=memory prof, trace=exec tracing, http=serve via net/http/pprof
--diagnostics-dir string directory to store diagnostics output files when not using http mode (defaults to current directory)