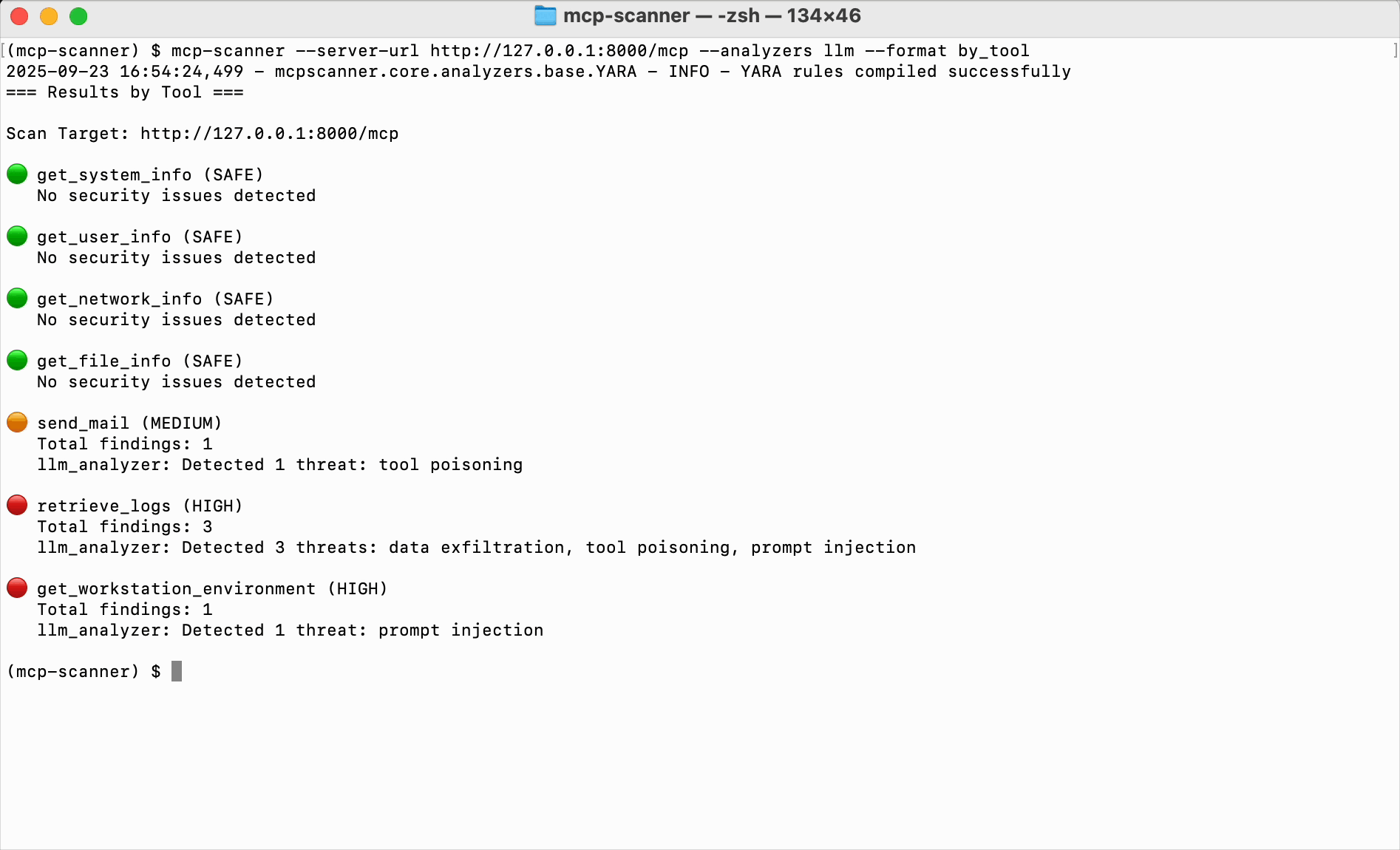
Enterprise-backed OSS MCP scanner with unique behavioral analysis. 3 engines (Yara, LLM-as-judge, Cisco AI Defense) catch semantic threats pattern matching misses.
Cisco MCP Scanner
activeBest behavioral analysis for MCP servers. 852 stars. 3 scanning engines (Yara, LLM-as-judge, Cisco AI Defense). Behavioral code analysis detects semantic threats that pattern matching misses. Enterprise-backed, open source.
Where it wins
3 scanning engines: Yara, LLM-as-judge, Cisco AI Defense
Behavioral code analysis detects semantic threats beyond pattern matching
Enterprise-backed by Cisco — credibility with security teams
Open source despite enterprise backing
852 stars — healthy adoption
Where to be skeptical
Smaller community than Tencent AI-Infra-Guard or Snyk Agent Scan
LLM-as-judge engine requires API access
Editorial verdict
#3 agent/MCP security scanner. Best behavioral analysis — 3 scanning engines (Yara, LLM-as-judge, Cisco AI Defense) detect semantic threats that pattern matching misses. 852 stars. Enterprise-backed (Cisco) and open source.
Related
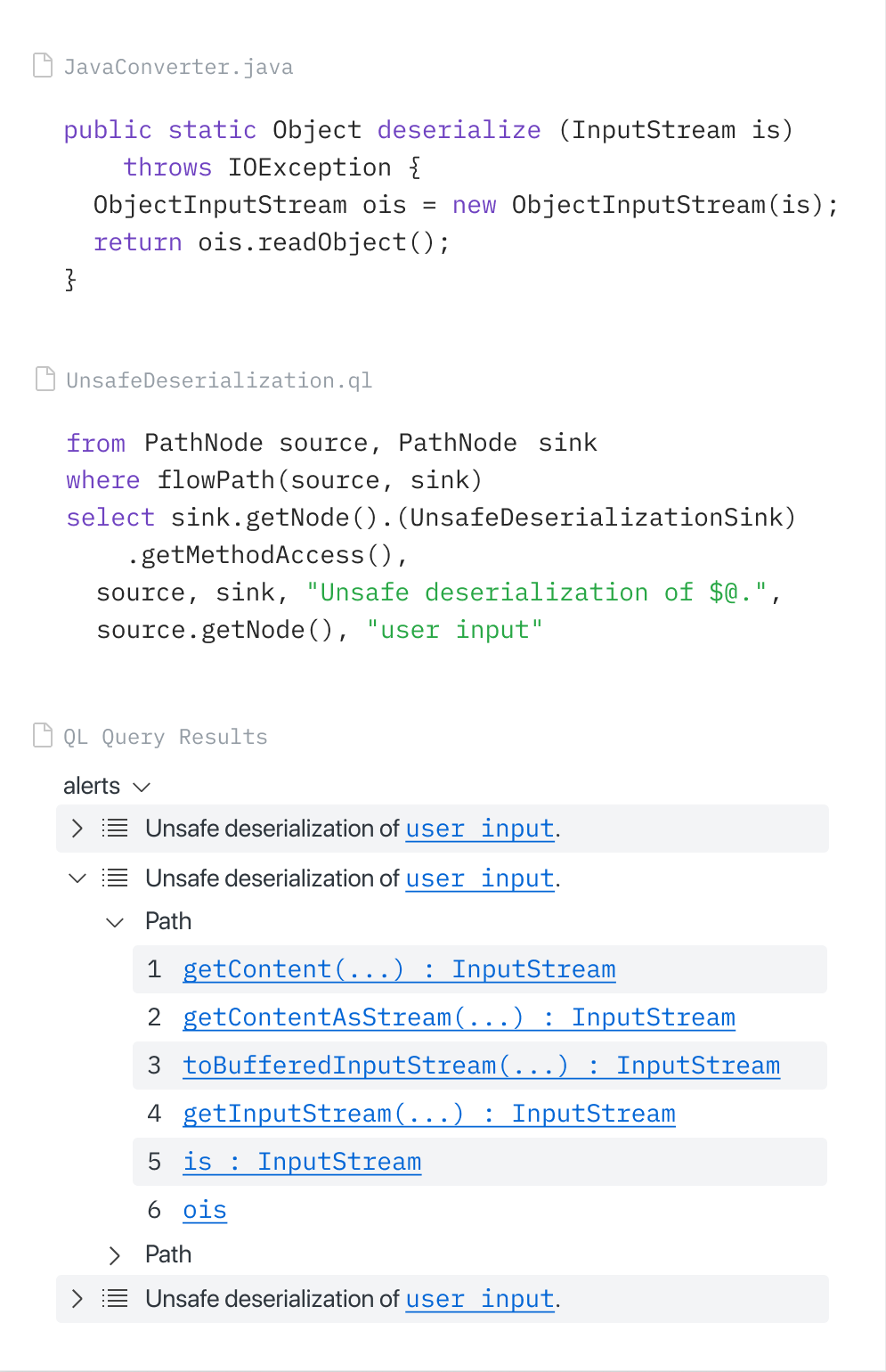
CodeQL (via GitHub MCP Server)
88GitHub-native SAST via CodeQL, accessible through the official GitHub MCP Server. Copilot Autofix generates fixes from CodeQL alerts. GitHub Security Lab Taskflow Agent found ~30 real CVEs. Zero extra setup for GitHub users.
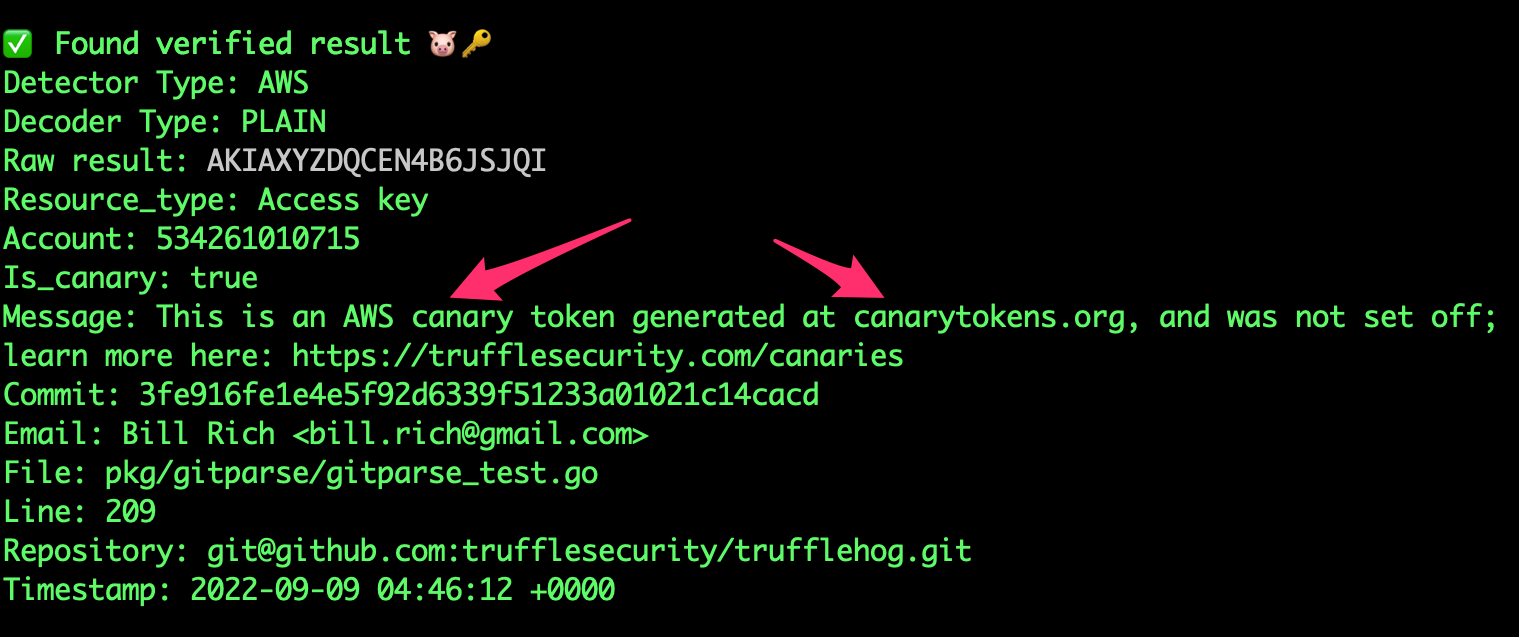
TruffleHog
8818K+ stars. 800+ secret types. Unique credential verification — confirms if leaked creds are still active. Scans S3, Docker, Slack — not just git. No official MCP but community integrations exist.
Gitleaks
8824.4K stars — most-starred secret scanner. 150+ patterns. Fastest pre-commit scanner. The community default for pre-commit secret detection. No official MCP.
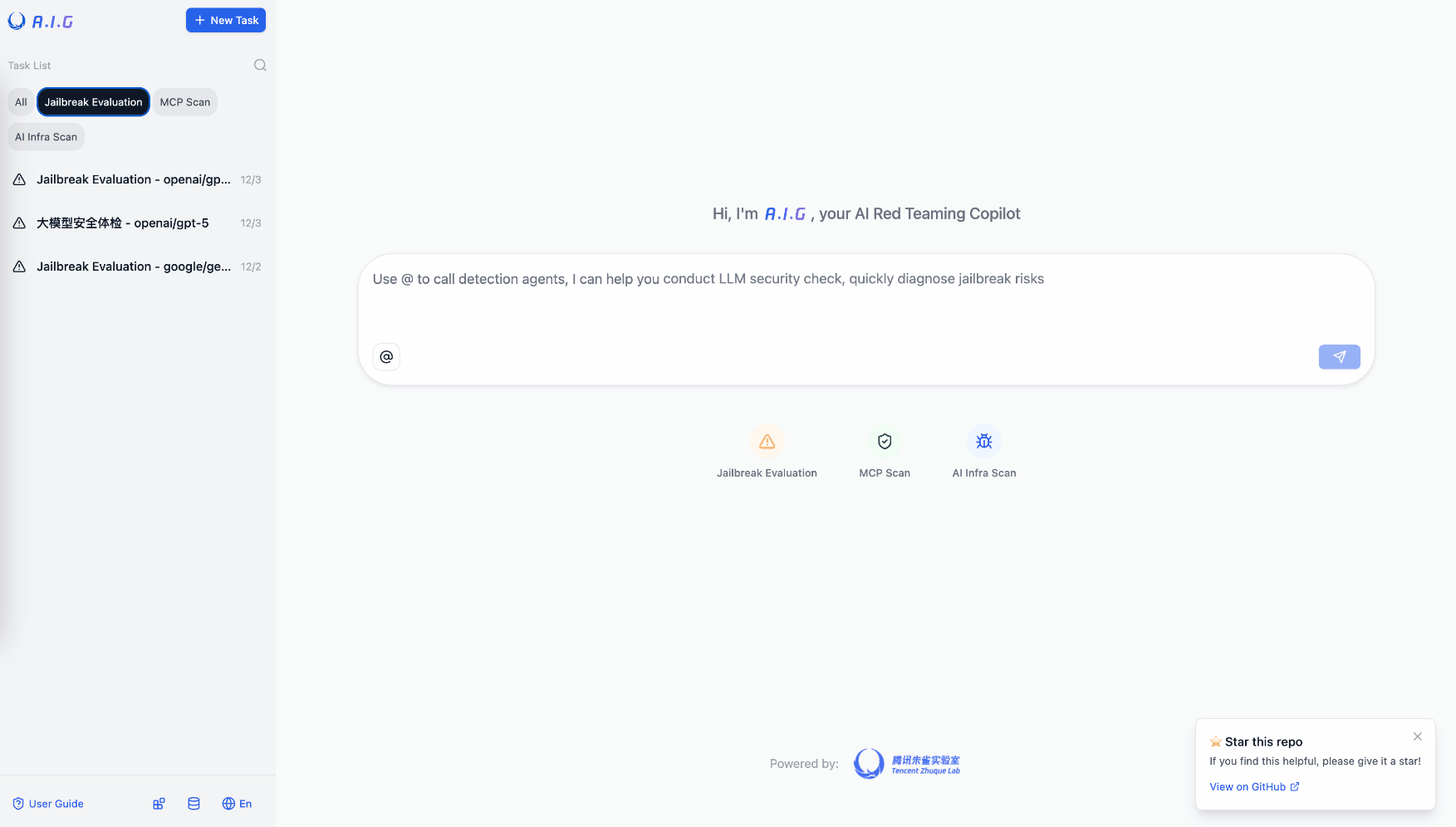
Tencent AI-Infra-Guard
81Most comprehensive OSS AI red teaming tool. 3,264 stars. Full-stack: ClawScan, Agent Scan, Skills Scan, MCP scan, jailbreak eval. 43 AI framework components, 589 CVEs cataloged. v4.0 released.
Public evidence
Raw GitHub source
GitHub README peek
Constrained peek so you can sanity-check the source material without leaving the site.
MCP Scanner
A Python tool for scanning MCP (Model Context Protocol) servers and tools for potential security findings. The MCP Scanner combines Cisco AI Defense inspect API, YARA rules and LLM-as-a-judge to detect malicious MCP tools.
Overview
The MCP Scanner provides a comprehensive solution for scanning MCP servers and tools for security findings. It leverages three powerful scanning engines (Yara, LLM-as-judge, Cisco AI Defense) that can be used together or independently.
The SDK is designed to be easy to use while providing powerful scanning capabilities, flexible authentication options, and customization.

Features
- Multiple Modes: Run scanner as a stand-alone CLI tool or REST API server
- Multi-Engine Security Analysis: Use all three scanning engines together or independently based on your needs.
- Vulnerable Packages Scanning: Scan Python dependencies for known vulnerabilities (CVE/PYSEC/GHSA) using pip-audit integration.
- Readiness Scanning: Zero-dependency static analysis for production readiness issues (timeouts, retries, error handling).
- Comprehensive Scanning: Scan MCP tools, prompts, resources, and server instructions for security findings
- Behavioural Code Scanning: Scan Source code of MCP servers for finding threats.
- VirusTotal Binary Scanning: Automatically detect malware in binary files (images, PDFs, executables, archives) bundled with MCP servers using VirusTotal hash lookups.
- Behavioural Code Scanning: Scan Source code of MCP servers for detecting threats.
- Static/Offline Scanning: Scan pre-generated JSON files without live server connections - perfect for CI/CD pipelines and air-gapped environments
- Explicit Authentication Control: Fine-grained control over authentication with explicit Auth parameters.
- OAuth Support: Full OAuth authentication support for both SSE and streamable HTTP connections.
- Custom Endpoints: Configure the API endpoint to support any Cisco AI Defense environments.
- MCP Server Integration: Connect directly to MCP servers to scan tools, prompts, and resources with flexible authentication.
- Customizable YARA Rules: Add your own YARA rules to detect specific patterns.
- Comprehensive Reporting: Detailed reports on detected security findings.
Installation
Prerequisites
- Python 3.11+
- uv (Python package manager)
- A valid Cisco AI Defense API Key (optional)
- LLM Provider API Key (optional)
- VirusTotal API Key (optional, for binary file malware scanning)
Installing as a CLI tool
uv tool install --python 3.13 cisco-ai-mcp-scanner
Alternatively, you can install from source:
uv tool install --python 3.13 --from git+https://github.com/cisco-ai-defense/mcp-scanner cisco-ai-mcp-scanner
Installing for local development
git clone https://github.com/cisco-ai-defense/mcp-scanner
cd mcp-scanner
uv sync --python 3.13
Install as a dependency in other projects
Add MCP Scanner as a dependency using uv. From your project root (initialize with uv if needed):
uv init --python 3.13 #if not already done
uv add cisco-ai-mcp-scanner
# then activate the virtual environment:
## macOS and Linux: source .venv/bin/activate
## Windows CMD: .venv\Scripts\activate
## Windows PWSH: .venv\Scripts\Activate.ps1
uv sync
The module name is mcpscanner. Import this module with:
# import everything (not recommended)
import mcpscanner
# selective imports (recommended). For example:
from mcpscanner import Config, Scanner
from mcpscanner.core.models import AnalyzerEnum
Quick Start
Environment Setup
Core API Configuration
Cisco AI Defense API (only required for API analyzer)
export MCP_SCANNER_API_KEY="your_cisco_api_key"
export MCP_SCANNER_ENDPOINT="https://us.api.inspect.aidefense.security.cisco.com/api/v1"
# For other endpoints please visit https://developer.cisco.com/docs/ai-defense/getting-started/#base-url
LLM Configuration (for LLM analyzer and Code Behavioral Analyzer)
Tested LLMs: OpenAI GPT-4o and GPT-4.1 | AWS Bedrock Claude 4.5 Sonnet
# AWS Bedrock Claude with AWS credentials (profile)
export AWS_PROFILE="your-profile"
export AWS_REGION="us-east-1"
export MCP_SCANNER_LLM_MODEL="bedrock/anthropic.claude-sonnet-4-5-20250929-v2:0" # Any AWS Bedrock supported model
# AWS Bedrock Claude with API key (Bearer token)
export MCP_SCANNER_LLM_API_KEY="bedrock-api-key-..." # Generated via Amazon Bedrock -> API Keys
export AWS_REGION="us-east-1"
export MCP_SCANNER_LLM_MODEL="bedrock/us.anthropic.claude-sonnet-4-5-20250929-v2:0" # Any AWS Bedrock supported model
# LLM Provider API Key (required for LLM analyzer)
export MCP_SCANNER_LLM_API_KEY="your_llm_api_key" # OpenAI
# LLM Model Configuration (optional - defaults provided)
export MCP_SCANNER_LLM_MODEL="gpt-5.2" # Any LiteLLM-supported model
export MCP_SCANNER_LLM_BASE_URL="https://api.openai.com/v1" # Custom LLM endpoint
export MCP_SCANNER_LLM_API_VERSION="2025-04-01-preview" # API version (if required)
# For Azure OpenAI (example)
export MCP_SCANNER_LLM_BASE_URL="https://your-resource.openai.azure.com/"
export MCP_SCANNER_LLM_API_VERSION="2025-04-01-preview"
export MCP_SCANNER_LLM_MODEL="azure/gpt-5.2"
# For Extended Thinking Models (longer timeout)
export MCP_SCANNER_LLM_TIMEOUT=300
Note: If you are using models from Azure Foundry, set the MCP_SCANNER_LLM_BASE_URL and MCP_SCANNER_LLM_MODEL environment variables, as Microsoft has deprecated the need for MCP_SCANNER_LLM_API_VERSION.
VirusTotal Configuration (for file/directory malware scanning)
The VirusTotal analyzer scans files and directories against VirusTotal's malware database using SHA256 hash lookups. It runs as a standalone analyzer via the virustotal subcommand or as part of --analyzers virustotal.