MCP servers for Nmap, Ghidra, Nuclei, SQLMap, Hashcat. Strongest on reverse engineering side. 481 stars.
FuzzingLabs Security Hub
activeMCP servers for Nmap, Ghidra, Nuclei, SQLMap, Hashcat. 481 stars. Stronger on reverse engineering and binary/protocol analysis. Best for security researchers doing binary work.
Where it wins
Reverse engineering focus — Ghidra integration via MCP
Binary and protocol analysis tools (Hashcat, Nuclei)
481 stars — niche but active
Where to be skeptical
Narrower than HexStrike or cyproxio collections
Reverse engineering focus limits general applicability
Editorial verdict
#3 offensive security. MCP servers for Nmap, Ghidra, Nuclei, SQLMap, Hashcat. 481 stars. Differentiates on reverse engineering / binary analysis. Best for security researchers working with binaries and protocols.
Related
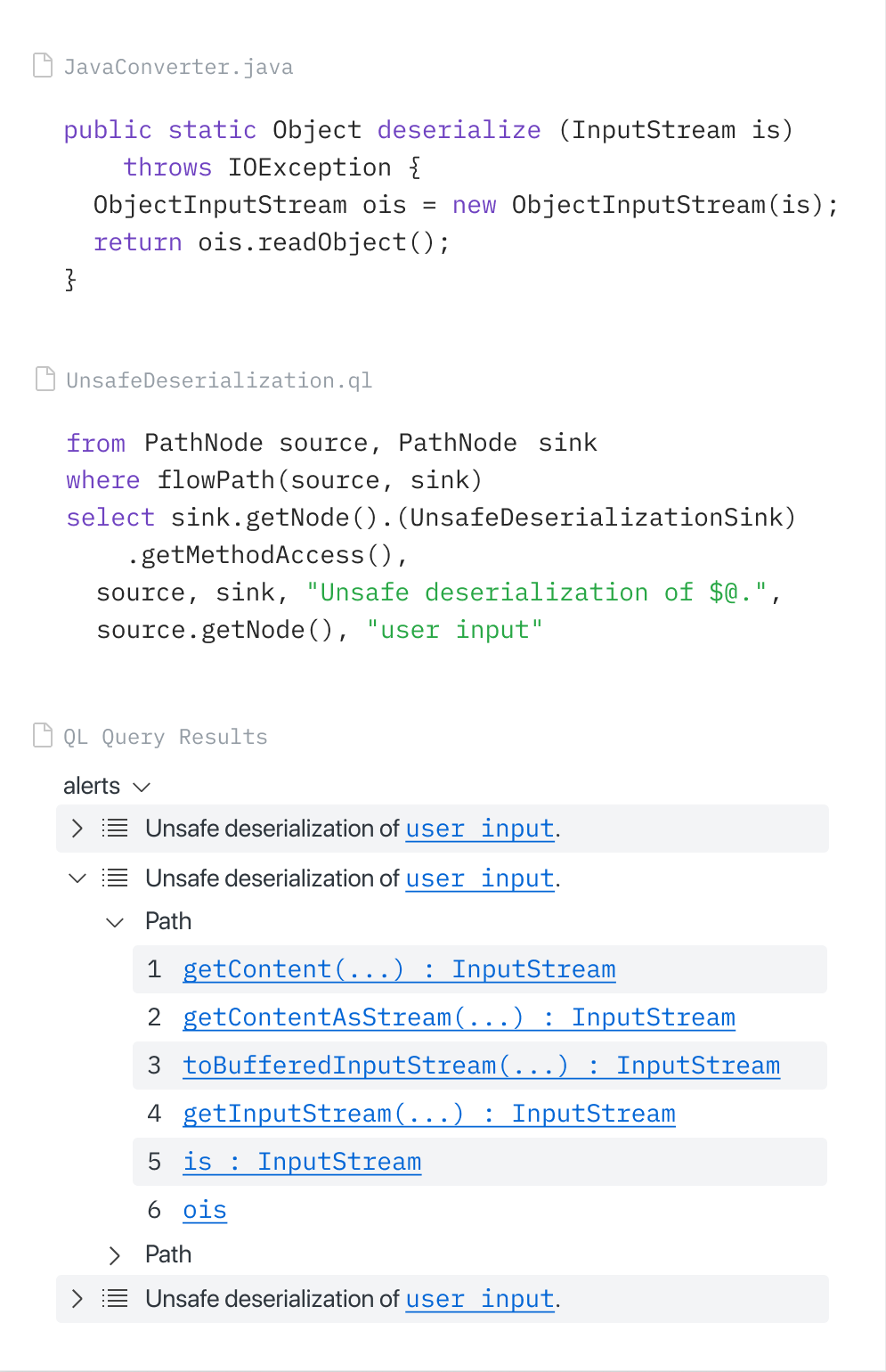
CodeQL (via GitHub MCP Server)
88GitHub-native SAST via CodeQL, accessible through the official GitHub MCP Server. Copilot Autofix generates fixes from CodeQL alerts. GitHub Security Lab Taskflow Agent found ~30 real CVEs. Zero extra setup for GitHub users.
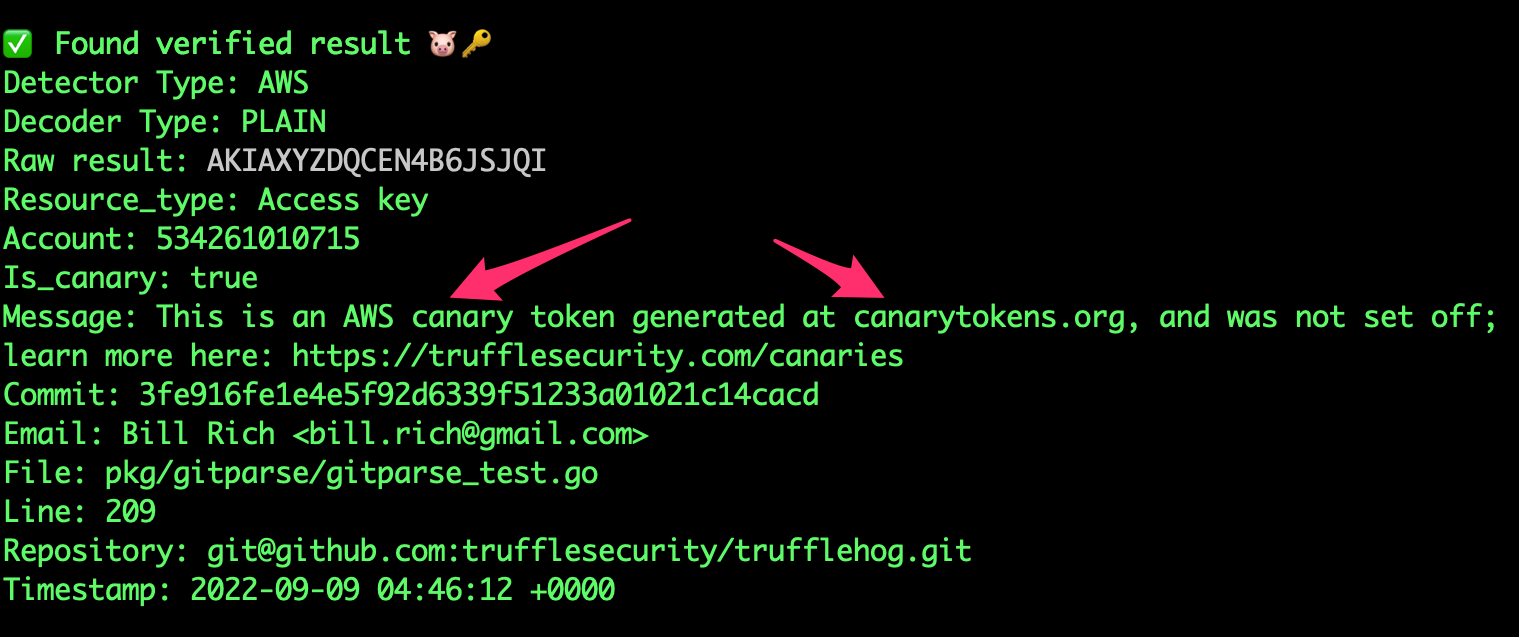
TruffleHog
8818K+ stars. 800+ secret types. Unique credential verification — confirms if leaked creds are still active. Scans S3, Docker, Slack — not just git. No official MCP but community integrations exist.
Gitleaks
8824.4K stars — most-starred secret scanner. 150+ patterns. Fastest pre-commit scanner. The community default for pre-commit secret detection. No official MCP.
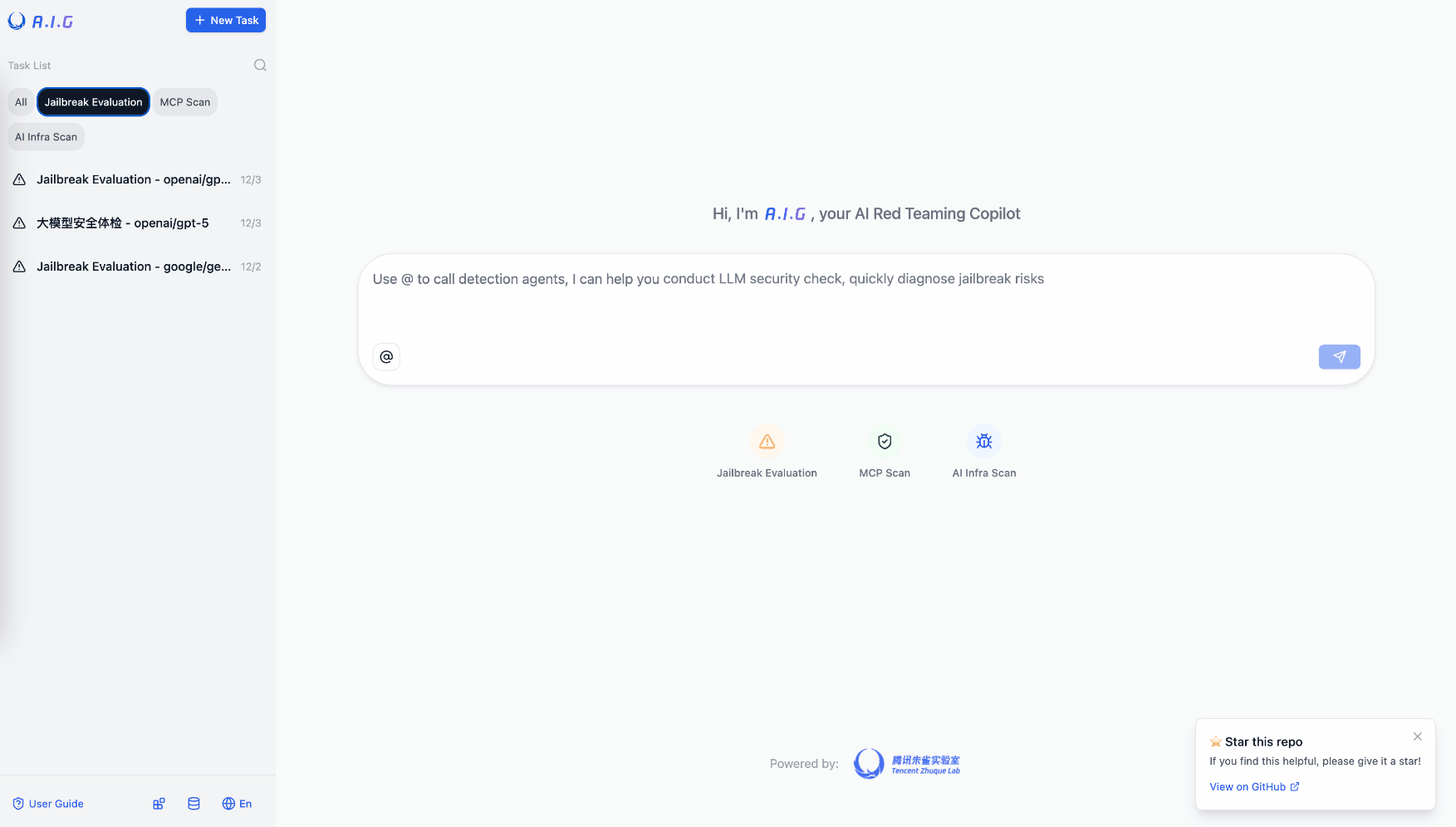
Tencent AI-Infra-Guard
81Most comprehensive OSS AI red teaming tool. 3,264 stars. Full-stack: ClawScan, Agent Scan, Skills Scan, MCP scan, jailbreak eval. 43 AI framework components, 589 CVEs cataloged. v4.0 released.
Public evidence
Raw GitHub source
GitHub README peek
Constrained peek so you can sanity-check the source material without leaving the site.
Offensive Security MCP Servers
Production-ready, Dockerized MCP (Model Context Protocol) servers for offensive security tools. Enable AI assistants like Claude to perform security assessments, vulnerability scanning, and binary analysis.
<p align="center"> </p>Features
- 38 MCP Servers covering reconnaissance, web security, binary analysis, blockchain security, cloud security, code security, secrets detection, threat intelligence, OSINT, Active Directory, fuzzing, and more
- 300+ Security Tools accessible via natural language through Claude or other MCP clients
- Production Hardened - Non-root containers, minimal images, Trivy-scanned
- Docker Compose orchestration for multi-tool workflows
- CI/CD Ready with GitHub Actions for automated builds and security scanning
Quick Start
# Clone the repository
git clone https://github.com/FuzzingLabs/mcp-security-hub
cd mcp-security-hub
# Build all MCP servers
docker-compose build
# Start specific servers
docker-compose up nmap-mcp nuclei-mcp -d
# Verify health
docker-compose ps
Configure Claude Desktop / Claude Code
Important: You must build the images first with docker-compose build before using them.
Copy the example config to your Claude Desktop configuration:
macOS: ~/Library/Application Support/Claude/claude_desktop_config.json
Windows: %APPDATA%\Claude\claude_desktop_config.json
{
"mcpServers": {
"nmap": {
"command": "docker",
"args": ["run", "-i", "--rm", "--cap-add=NET_RAW", "nmap-mcp:latest"]
},
"nuclei": {
"command": "docker",
"args": ["run", "-i", "--rm", "nuclei-mcp:latest"]
},
"gitleaks": {
"command": "docker",
"args": ["run", "-i", "--rm", "-v", "/path/to/repos:/app/target:ro", "gitleaks-mcp:latest"]
},
"radare2": {
"command": "docker",
"args": ["run", "-i", "--rm", "-v", "/path/to/binaries:/samples:ro", "radare2-mcp:latest"]
}
}
}
For project-level config, copy .mcp.json to your project root. See examples/ for full configuration templates with all MCPs and volume mount patterns.
Available MCP Servers
Reconnaissance (8 servers)
| Server | Tools | Description |
|---|---|---|
| nmap-mcp | 8 | Port scanning, service detection, OS fingerprinting, NSE scripts |
| shodan-mcp | - | Wrapper for official Shodan MCP |
| pd-tools-mcp | - | Wrapper for ProjectDiscovery tools (subfinder, httpx, katana) |
| whatweb-mcp | 5 | Web technology fingerprinting and CMS detection |
| masscan-mcp | 6 | High-speed port scanning for large networks |
| zoomeye-mcp | - | Wrapper for ZoomEye MCP - Cyberspace search engine |
| networksdb-mcp | 4 | IP/ASN/DNS lookups via NetworksDB |
| externalattacker-mcp | 6 | Attack surface mapping with ExternalAttacker |
Web Security (6 servers)
| Server | Tools | Description |
|---|---|---|
| nuclei-mcp | 7 | Template-based vulnerability scanning with 8000+ templates |
| sqlmap-mcp | 8 | SQL injection detection and exploitation |
| nikto-mcp | - | Wrapper for Nikto MCP web server scanner |
| ffuf-mcp | 9 | Web fuzzing for directories, files, parameters, and virtual hosts |
| waybackurls-mcp | 3 | Fetch historical URLs from Wayback Machine for reconnaissance |
| burp-mcp | - | Wrapper for official Burp Suite MCP |
Binary Analysis (6 servers)
| Server | Tools | Description |
|---|---|---|
| radare2-mcp | 32 | Wrapper for official radare2-mcp - disassembly, decompilation |
| binwalk-mcp | 6 | Firmware analysis, signature scanning, extraction |
| yara-mcp | 7 | Pattern matching for malware classification |
| capa-mcp | 5 | Capability detection in executables |
| ghidra-mcp | - | Wrapper for pyghidra-mcp - Headless AI-powered reverse engineering |
| ida-mcp | - | Wrapper for ida-pro-mcp - IDA Pro integration |
Blockchain Security (3 servers)
| Server | Tools | Description |
|---|---|---|
| daml-viewer-mcp | 1 | DAML access-control table generation and run tracking |
| medusa-mcp | 4 | High-performance smart contract fuzzer for Solidity |
| solazy-mcp | 8 | Solana sBPF static analysis and reverse engineering |
Cloud Security (3 servers)
| Server | Tools | Description |
|---|---|---|
| trivy-mcp | 7 | Container, filesystem, and IaC vulnerability scanning |
| prowler-mcp | 6 | AWS/Azure/GCP security auditing and compliance |
| roadrecon-mcp | 6 | Azure AD enumeration via RoadRecon |
Secrets Detection (1 server)
| Server | Tools | Description |
|---|---|---|
| gitleaks-mcp | 5 | Find secrets and credentials in git repos and files |
Exploitation (1 server)
| Server | Tools | Description |
|---|---|---|
| searchsploit-mcp | 5 | Exploit-DB search and retrieval |
Fuzzing (2 servers)
| Server | Tools | Description |
|---|---|---|
| boofuzz-mcp | 4 | Network protocol fuzzing using Boofuzz |