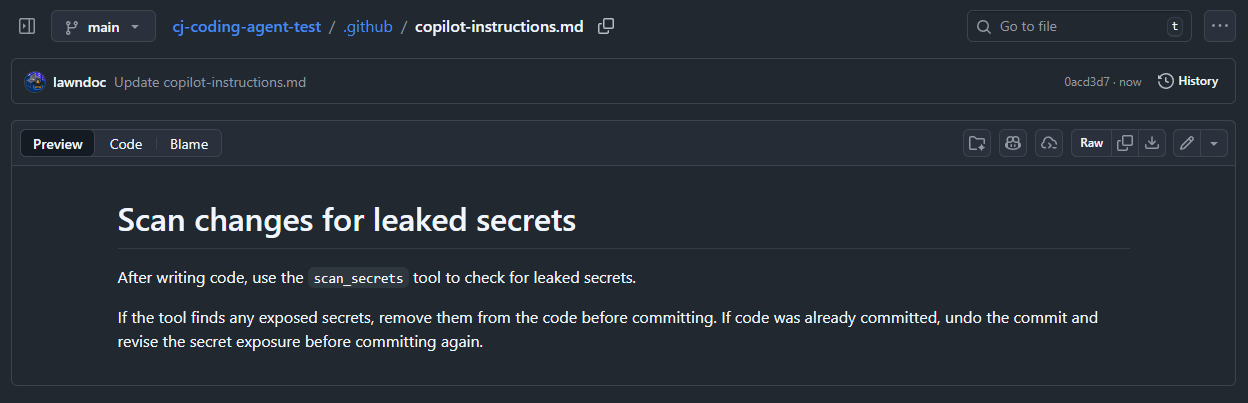
Definitive annual report on secret sprawl. 81% surge in AI-service key leaks. 24,008 secrets found in MCP configurations. Quantifies the problem that secret scanning MCP tools solve.
GitGuardian MCP (ggmcp)
activeBest purpose-built secret scanning MCP. 500+ detectors. Hard merge gate for AI-generated code. State of Secrets Sprawl 2026 report documents 81% surge in AI-service key leaks and 24,008 secrets found in MCP configs.
Where it wins
500+ secret detectors — broadest coverage in the category
Hard merge gate for AI-generated code — blocks secrets before they land
State of Secrets Sprawl 2026 report — definitive industry research on secret leaks
81% surge in AI-service key leaks documented — proves the problem this tool solves
24,008 secrets found in MCP configs — directly relevant to agent security
Official MCP server (ggmcp) — first-class agent integration
Where to be skeptical
Commercial platform — free tier exists but full features require subscription
MCP server community size smaller than Gitleaks or TruffleHog OSS projects
Editorial verdict
#1 secret detection. Purpose-built secret scanning MCP with 500+ detectors and hard merge gates for AI-generated code. State of Secrets Sprawl 2026 report (81% surge in AI-service key leaks, 24,008 secrets in MCP configs) is the definitive source on the problem. The default recommendation for secret scanning in agent workflows.
Related
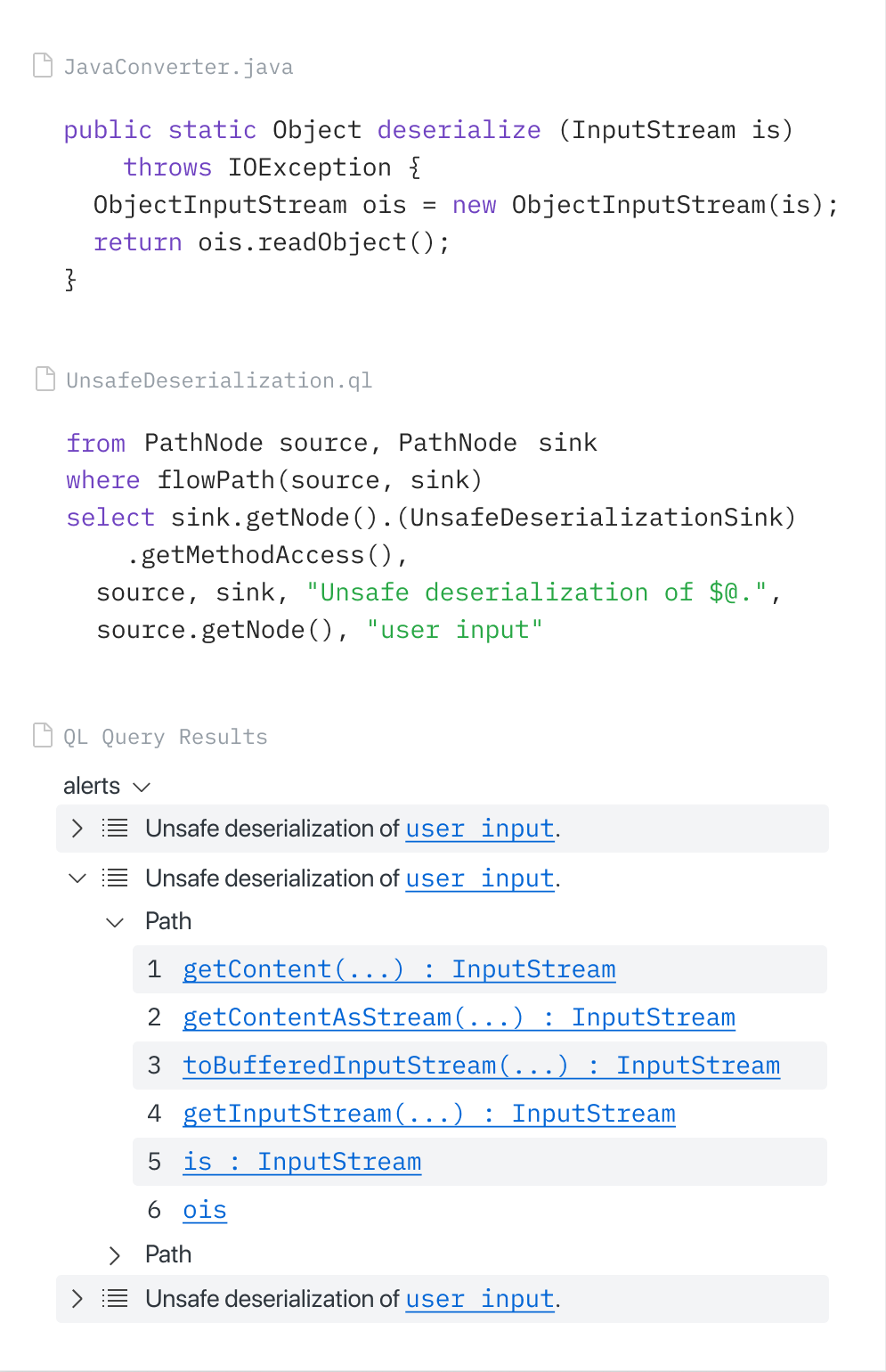
CodeQL (via GitHub MCP Server)
88GitHub-native SAST via CodeQL, accessible through the official GitHub MCP Server. Copilot Autofix generates fixes from CodeQL alerts. GitHub Security Lab Taskflow Agent found ~30 real CVEs. Zero extra setup for GitHub users.
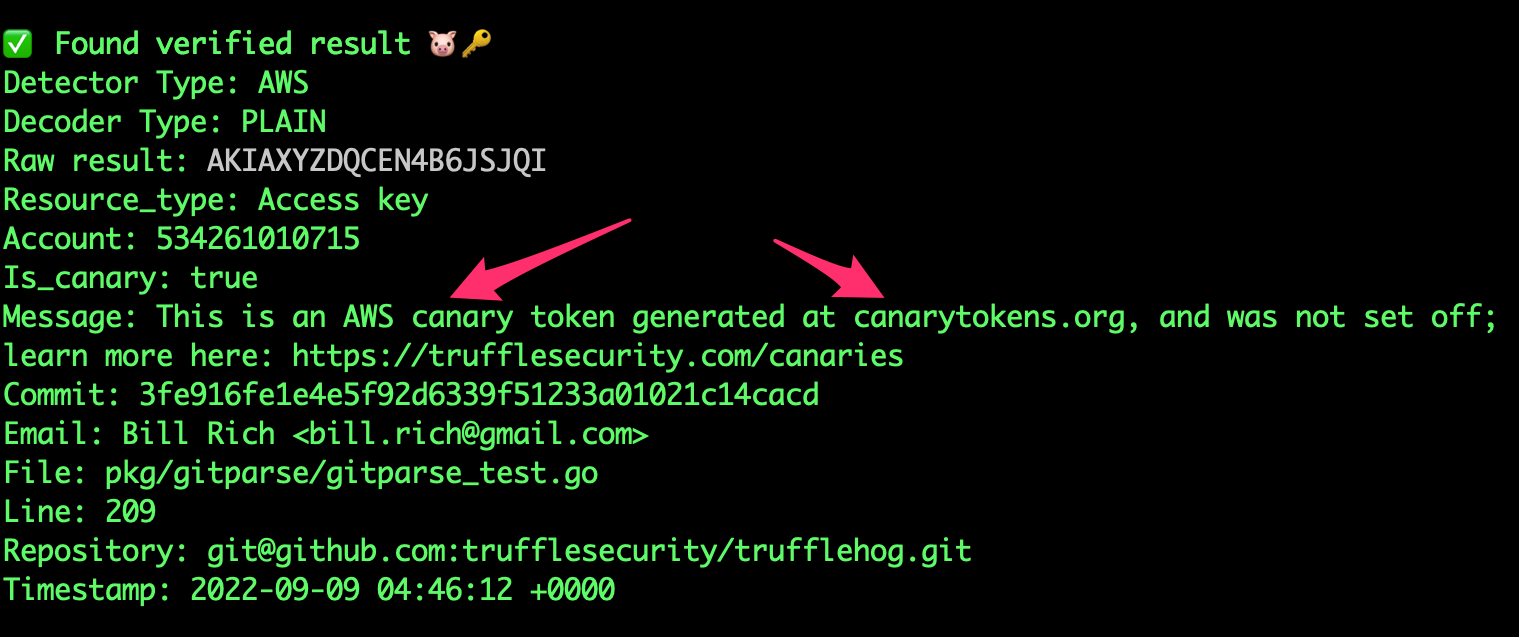
TruffleHog
8818K+ stars. 800+ secret types. Unique credential verification — confirms if leaked creds are still active. Scans S3, Docker, Slack — not just git. No official MCP but community integrations exist.
Gitleaks
8824.4K stars — most-starred secret scanner. 150+ patterns. Fastest pre-commit scanner. The community default for pre-commit secret detection. No official MCP.
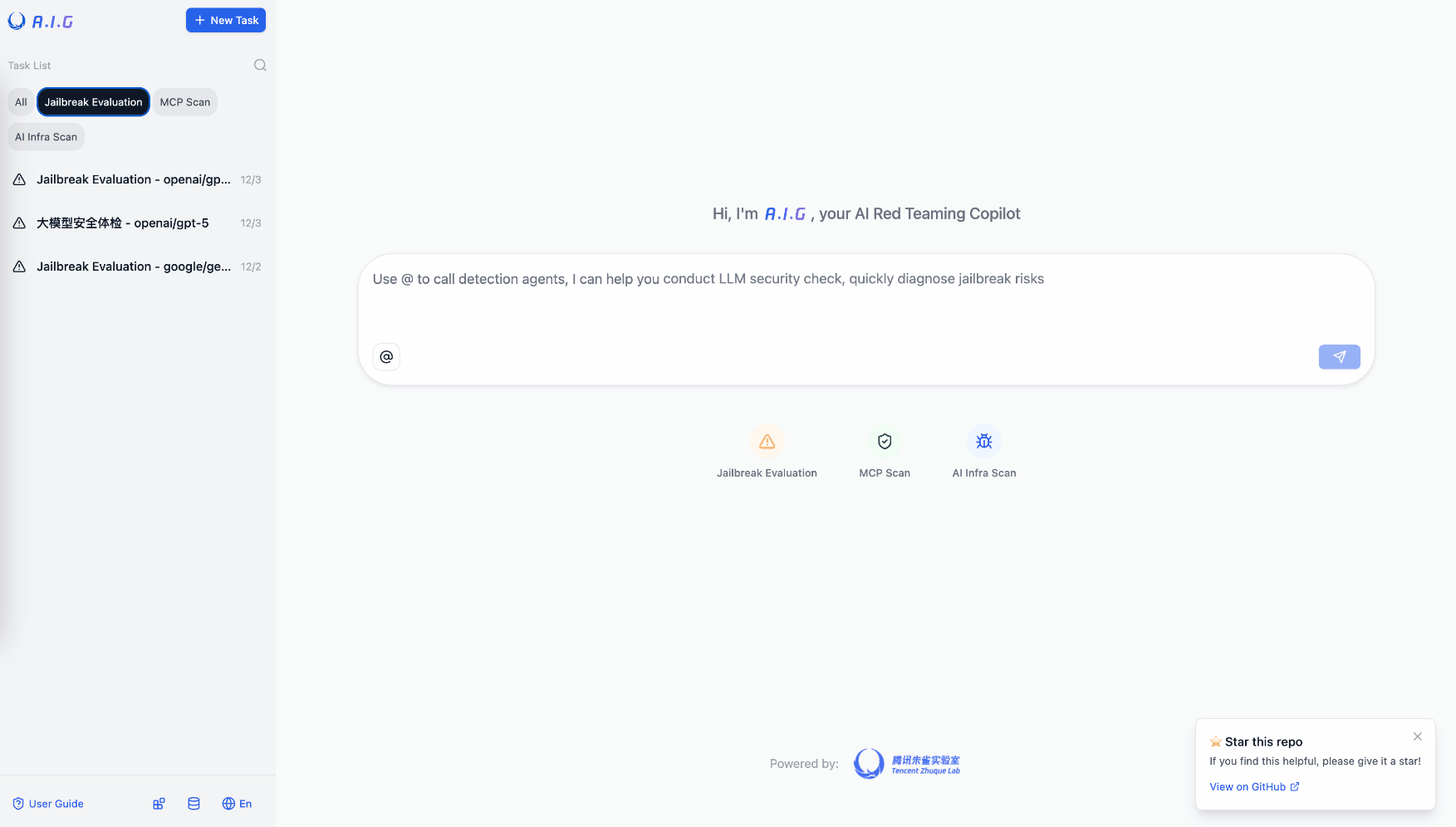
Tencent AI-Infra-Guard
81Most comprehensive OSS AI red teaming tool. 3,264 stars. Full-stack: ClawScan, Agent Scan, Skills Scan, MCP scan, jailbreak eval. 43 AI framework components, 589 CVEs cataloged. v4.0 released.
Public evidence
Official MCP server for GitGuardian. 500+ secret detectors. Hard merge gate blocks secrets in AI-generated code before they reach the repository.
Raw GitHub source
GitHub README peek
Constrained peek so you can sanity-check the source material without leaving the site.
GitGuardian MCP Server
Stay focused on building your product while your AI assistant handles the security heavy lifting with GitGuardian's comprehensive protection.
This MCP server enables your AI agent to scan projects using GitGuardian's industry-leading API, featuring over 500 secret detectors to prevent credential leaks before they reach public repositories.
Resolve security incidents without context switching to the GitGuardian console. Take advantage of rich contextual data to enhance your agent's remediation capabilities, enabling rapid resolution and automated removal of hardcoded secrets.
Disclaimer
[!CAUTION] MCP servers are an emerging and rapidly evolving technology. While they can significantly boost productivity and improve the developer experience, their use with various agents and models should always be supervised.
Agents act on your behalf and under your responsibility. Always use MCP servers from trusted sources (just as you would with any dependency), and carefully review agent actions when they interact with MCP server tools.
To better assist you in safely using this server, we have:
(1) Designed our MCP server to operate with "read-only" permissions, minimizing the access level granted to your agent. This helps ensure that, even if the agent tries to perform unintended actions, its capabilities remain limited to safe, non-destructive operations.
(2) Released this official MCP server to ensure you are using a legitimate and trusted implementation.
Features supported
- Secret Scanning: Scan code for leaked secrets, credentials, and API keys
- Incident Management: View security incidents related to the project you are currently working.
- Honeytokens: Create honeytokens to detect unauthorized access
- Authentication Management: Get authenticated user information and token details
- Token Management: Revoke current API tokens
Want more features? Have a use case that's not covered? We'd love to hear from you! Submit your ideas and feedback by opening an issue on GitHub to help us prioritize new MCP server capabilities.
Prompts examples
Remediate all incidents related to my project
Scan this codebase for any leaked secrets or credentials
Check if there are any new security incidents assigned to me
Help me understand this security incident and provide remediation steps
List all my active honeytokens
Generate a new honeytoken for monitoring AWS credential access
Show me my most recent honeytoken and help me embed it in my codebase
Create a honeytoken named 'dev-database' and hide it in config files
Prerequisites
Before installing the GitGuardian MCP servers, ensure you have the following prerequisites:
- uv: This project uses uv for package installation and dependency management. Install uv by following the instructions at: https://docs.astral.sh/uv/getting-started/installation/
Installation
Below are instructions for installing the GitGuardian MCP servers with various AI editors and interfaces.
The MCP server supports both GitGuardian SaaS and self-hosted instances.
Installation with Cursor
Quick Install with One-Click Buttons (Cursor >= 1.0):
Note: The one-click install sets up the default US SaaS configuration. For EU SaaS or self-hosted instances, you'll need to manually add environment variables as shown in the Configuration section. A single MCP server now serves both developer and SecOps audiences — the tools exposed to your agent depend on the OAuth scopes granted to the access token. The deprecated
developer-mcp-serverandsecops-mcp-serverentry points still work for one release but emit aDeprecationWarning; migrate togg-mcp-server.
Manual Configuration:
-
Edit your Cursor MCP configuration file located at
~/.cursor/mcp.json -
Add the GitGuardian MCP server configuration:
{ "mcpServers": { "GitGuardian": { "command": "uvx", "args": [ "--from", "git+https://github.com/GitGuardian/ggmcp.git", "gg-mcp-server" ] } } }
Installation with Claude Desktop
-
Edit your Claude Desktop MCP configuration file located at:
- macOS:
~/Library/Application Support/Claude Desktop/mcp.json - Windows:
%APPDATA%\Claude Desktop\mcp.json
- macOS:
-
Add the GitGuardian MCP server configuration:
{ "mcpServers": { "GitGuardian": { "command": "/path/to/uvx", "args": [ "--from", "git+https://github.com/GitGuardian/ggmcp.git", "gg-mcp-server" ] } } } -
Replace
/path/to/uvxwith the absolute path to the uvx executable on your system.⚠️ WARNING: For Claude Desktop, you must specify the full absolute path to the
uvxexecutable, not just"command": "uvx". This is different from other MCP clients. -
Restart Claude Desktop to apply the changes.
Installation with Windsurf
To use the GitGuardian MCP server with Windsurf:
-
Edit your Windsurf MCP configuration file located at:
- macOS:
~/Library/Application Support/Windsurf/mcp.json - Windows:
%APPDATA%\Windsurf\mcp.json - Linux:
~/.config/Windsurf/mcp.json
- macOS:
-
Add the following entry to the configuration file:
{ "mcp": { "servers": { "GitGuardian": { "type": "stdio", "command": "uvx",