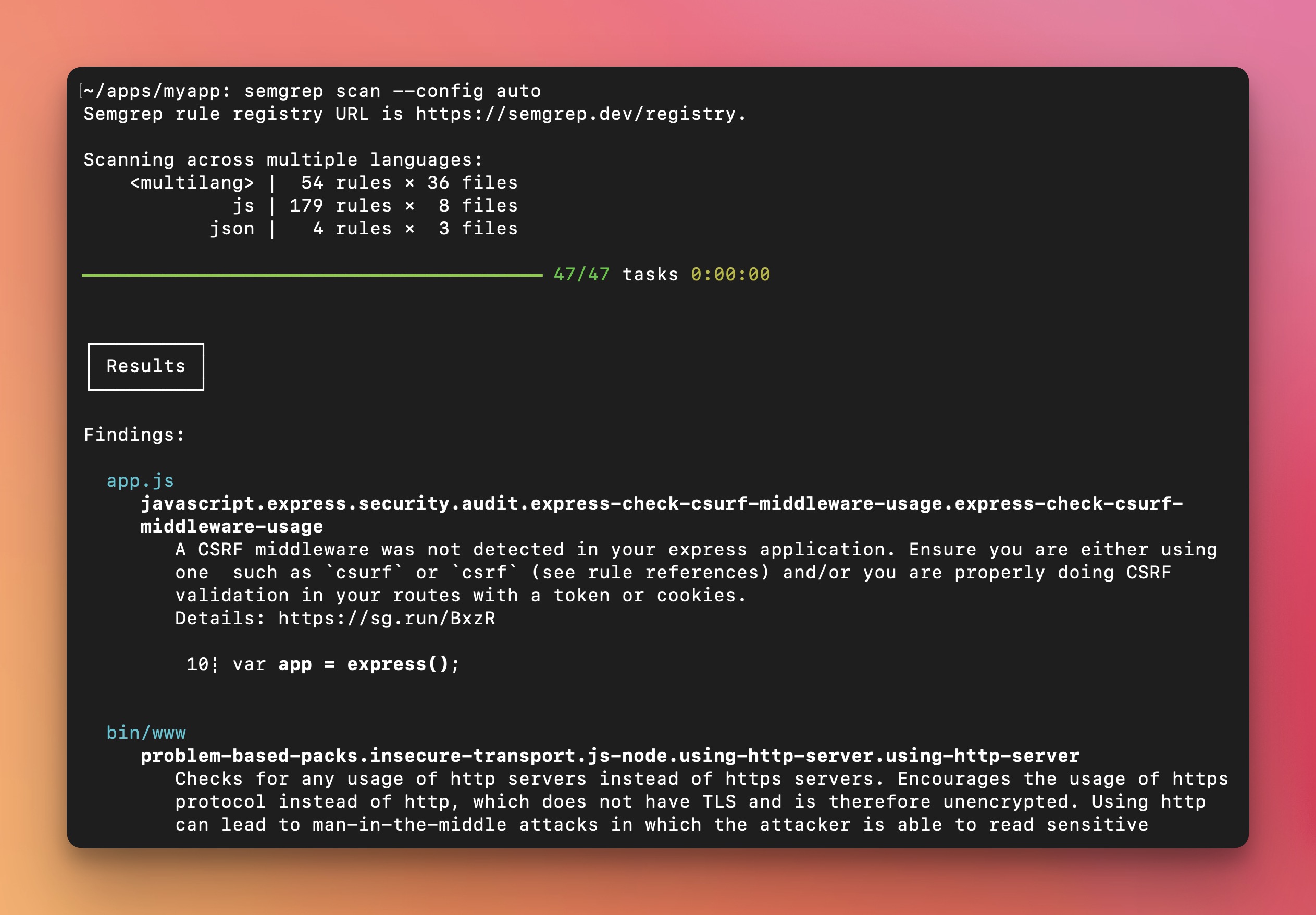
Semgrep detected 46% of vulnerabilities out-of-box vs SonarQube 19%. DryRun's own tool hit 88%. First credible cross-tool SAST benchmark for agent workflows.
Semgrep MCP
activeOfficial Semgrep MCP server. Best-in-class OSS SAST with 46% vuln detection (DryRun benchmark) vs SonarQube 19%. AST-based rules are transparent and auditable. LinkedIn rebuilt their SAST pipeline around it (Feb 2026). Mindshare rising 1.6% → 2.6%.
Where it wins
Official MCP server — first-class agent integration
46% vuln detection in DryRun benchmark (vs SonarQube 19%) — strongest independent SAST result
AST-based rules are transparent and auditable — no black-box scanning
LinkedIn rebuilt SAST pipeline around Semgrep (Feb 2026) — enterprise validation
Mindshare rising from 1.6% to 2.6% — growing category share
OSS with commercial tier — no vendor lock-in on the core scanning engine
Where to be skeptical
DryRun benchmark shows 88% detection for DryRun's own tool — Semgrep trails on raw detection rate
MCP server is relatively new — smaller community integrations vs the main Semgrep CLI
Commercial features (Supply Chain, Secrets) require paid tier
Editorial verdict
#1 SAST skill. Best-in-class OSS SAST with official MCP server. 46% vuln detection in DryRun benchmark (vs SonarQube 19%). AST-based rules are transparent and auditable. Rising mindshare (1.6% → 2.6%). LinkedIn rebuilt SAST pipeline around it. The default recommendation for code scanning via AI agents.
Source
Related
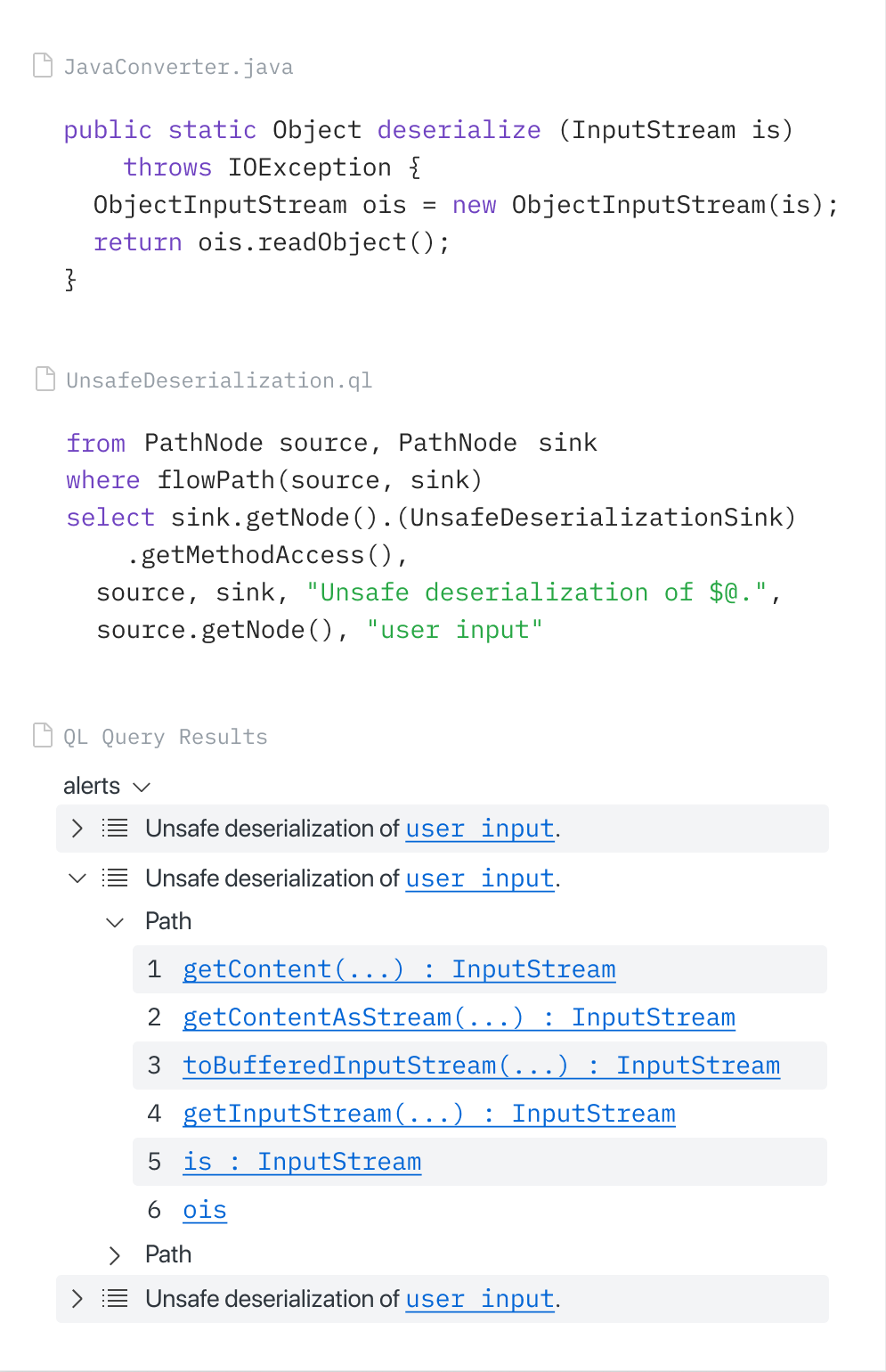
CodeQL (via GitHub MCP Server)
88GitHub-native SAST via CodeQL, accessible through the official GitHub MCP Server. Copilot Autofix generates fixes from CodeQL alerts. GitHub Security Lab Taskflow Agent found ~30 real CVEs. Zero extra setup for GitHub users.
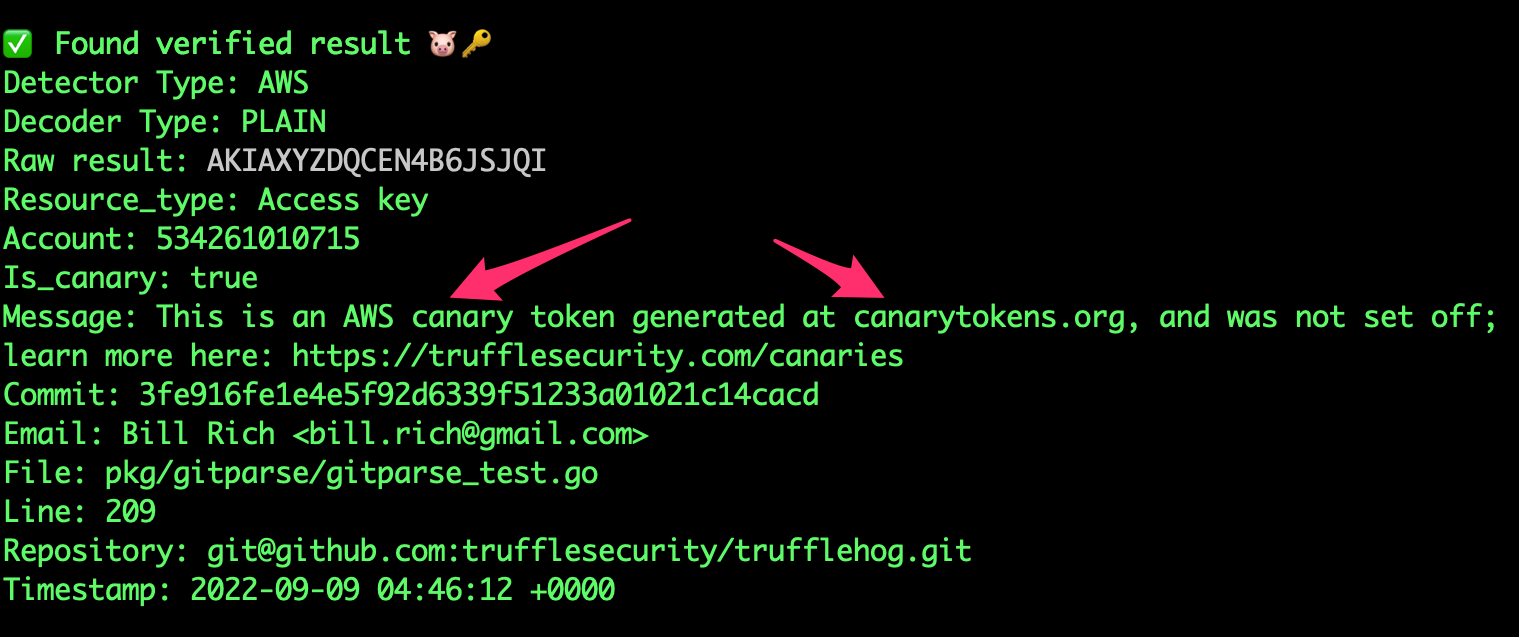
TruffleHog
8818K+ stars. 800+ secret types. Unique credential verification — confirms if leaked creds are still active. Scans S3, Docker, Slack — not just git. No official MCP but community integrations exist.
Gitleaks
8824.4K stars — most-starred secret scanner. 150+ patterns. Fastest pre-commit scanner. The community default for pre-commit secret detection. No official MCP.
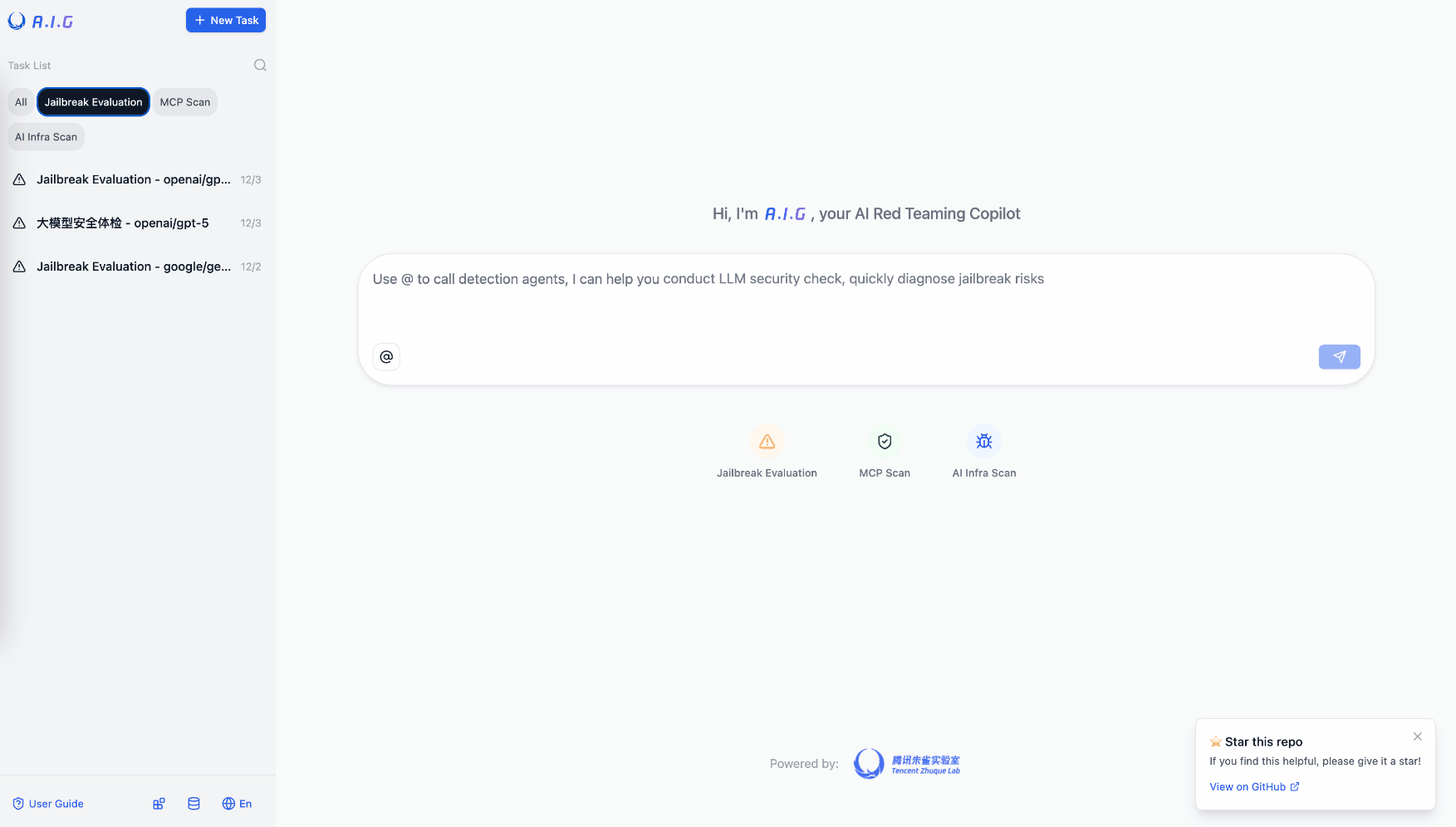
Tencent AI-Infra-Guard
81Most comprehensive OSS AI red teaming tool. 3,264 stars. Full-stack: ClawScan, Agent Scan, Skills Scan, MCP scan, jailbreak eval. 43 AI framework components, 589 CVEs cataloged. v4.0 released.
Public evidence
LinkedIn replaced prior SAST tooling with Semgrep as the core scanning engine. Enterprise-scale validation of Semgrep's rule quality and performance.
Official MCP server maintained by Semgrep. 641 stars indicates healthy early adoption for a purpose-built MCP integration.
Raw GitHub source
GitHub README peek
Constrained peek so you can sanity-check the source material without leaving the site.
⚠️ The Semgrep MCP server has been moved from a standalone repo to the main semgrep repository! ⚠️
This repository has been deprecated, and further updates to the Semgrep MCP server will be made via the official semgrep binary.
Semgrep MCP Server
A Model Context Protocol (MCP) server for using Semgrep to scan code for security vulnerabilities. Secure your vibe coding! 😅
Model Context Protocol (MCP) is a standardized API for LLMs, Agents, and IDEs like Cursor, VS Code, Windsurf, or anything that supports MCP, to get specialized help, get context, and harness the power of tools. Semgrep is a fast, deterministic static analysis tool that semantically understands many languages and comes with over 5,000 rules. 🛠️
[!NOTE] This beta project is under active development. We would love your feedback, bug reports, feature requests, and code. Join the
#mcpcommunity Slack channel!
Contents
- Semgrep MCP Server
- Contents
- Getting started
- Cursor
- ChatGPT
- Hosted Server
- Cursor
- Demo
- API
- Tools
- Scan Code
- Understand Code
- Cloud Platform (login and Semgrep token required)
- Meta
- Prompts
- Resources
- Tools
- Usage
- Standard Input/Output (stdio)
- Python
- Docker
- Streamable HTTP
- Python
- Docker
- Server-sent events (SSE)
- Python
- Docker
- Standard Input/Output (stdio)
- Semgrep AppSec Platform
- Integrations
- Cursor IDE
- VS Code / Copilot
- Manual Configuration
- Using Docker
- Windsurf
- Claude Desktop
- Claude Code
- OpenAI
- Agents SDK
- Custom clients
- Example Python SSE client
- Contributing, community, and running from source
- Similar tools 🔍
- Community projects 🌟
- MCP server registries
Getting started
Run the Python package as a CLI command using uv:
uvx semgrep-mcp # see --help for more options
Or, run as a Docker container:
docker run -i --rm ghcr.io/semgrep/mcp -t stdio
Cursor
Example mcp.json
{
"mcpServers": {
"semgrep": {
"command": "uvx",
"args": ["semgrep-mcp"],
"env": {
"SEMGREP_APP_TOKEN": "<token>"
}
}
}
}
Add an instruction to your .cursor/rules to use automatically:
Always scan code generated using Semgrep for security vulnerabilities
ChatGPT
- Go to the Connector Settings page (direct link)
- Name the connection
Semgrep - Set MCP Server URL to
https://mcp.semgrep.ai/sse - Set Authentication to
No authentication - Check the I trust this application checkbox
- Click Create
See more details at the official docs.
Hosted Server
[!WARNING] mcp.semgrep.ai is an experimental server that may break unexpectedly. It will rapidly gain new functionality.🚀
Cursor
- Cmd + Shift + J to open Cursor Settings
- Select MCP Tools
- Click New MCP Server.